Top Tactics to Protect Your VoIP from Phishing and Vishing Attacks
Vishing attacks often make the news. Recently, scammers impersonated online retail giant Amazon, sending emails about fake orders and then demanding credit card numbers when individuals called to get a refund.
These scams are on the rise, and they pose a threat not only to individuals, but also to businesses. The FBI even issued a warning in January 2021, encouraging businesses to be more vigilant about security risks associated with vishing attacks.
The FBI noted that vishing scammers have moved beyond targeting only high-level employees with more extensive access. Vishing attacks might now focus on convincing any employee to share credentials, which can then be used to gain greater access to those in the employee’s network.
Although vishing certainly poses a threat to organizations, the right security measures can help protect your company and employees.
What Is Vishing?
Most of us are familiar with phishing, which uses email to lure unsuspecting people into sharing sensitive information like bank account and credit card numbers or usernames and passwords. Vishing adds a voice component to that strategy. The perpetrator might either call people directly, or send an email with a spoof contact number.
Vishing relies on social engineering to manipulate people into sharing that sensitive information. These tactics are common:
- False urgency: The caller insists that the target must comply or face immediate, dire consequences. For example, in one vishing attack, scammers impersonated the United States Internal Revenue Service and insisted that people must immediately pay a fake tax bill or face a lawsuit.
- Impossible promises: We’re all familiar with get-rich-quick schemes, which are still a favorite tactic for vishing attacks. These are less common in the context of businesses, but it’s important for employees to remain aware.
- Pretexting: The caller pretends to need critical information to perform some critical task. This starts with the impersonation of a trusted authority--which might even include someone from inside the organization, such as an IT or help-desk employee.
To enhance legitimacy, perpetrators might imitate the email or phone number of a trusted source. This practice is known as spoofing. For instance, in the Amazon vishing attacks, emails that closely resembled actual Amazon email addresses were used.
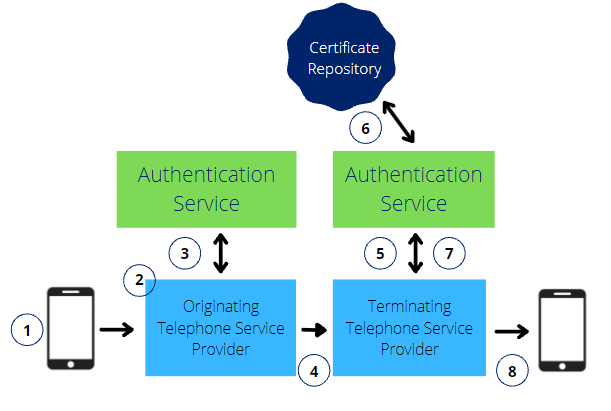
Phone numbers can also be spoofed, a practice that is illegal in the United States. But it isn’t as regulated elsewhere, so perpetrators might call from overseas using VoIP. The same low-cost international calling that makes VoIP appealing for your business also makes it attractive for vishing scammers.
How to Protect Your Organization Against Vishing Attacks
Vishing attacks have gotten more sophisticated, so everyone in an organization must be vigilant about security. These seven strategies can help protect your company and your employees.
#1. Segment the Network
The standard network is one giant, interconnected system where every member belongs to the same “pool.” That might be the easiest to set up and monitor; however it’s also quite vulnerable because everyone is open to an attack via any user.
Instead, consider segmenting your network. This way, if the network is infiltrated, it will only put a limited number of members or users at risk rather than the entire organization. Each segment should be closely monitored for unusual activity or unauthorized access.
#2. Use the Principle of Least Privilege
Many organizations still use role-based access to their networks and applications, that is, anyone who’s a manager gets certain access privileges. This means that people often have more access than they need, unnecessarily increasing risk.
In contrast, the principle of least privilege dictates that employees get the least amount of access needed to do their jobs. This approach means that access is assigned dynamically as a response to changing responsibilities, workloads, and risk factors.
#3. Monitor VPN Access
Following the principle of least privilege, VPN access would ideally be limited to certain users. But that often isn’t possible in today’s remote work environment. Closely monitor VPN certificates to ensure that only authorized users are accessing the network via VPN.
Another way to limit the risk of unauthorized VPN access is to limit the hours when VPN is available. Blocking VPN access overnight, for example, can help prevent attacks from overseas.
#4. Implement Multi-Factor Authentication
Multi-Factor Authentication requires a user to provide at least two verification factors to access an account or resource. For instance, the second authentication might be a one-time code that a user receives via automated text or email upon entering the correct username and password.
Because that second authentication factor can’t be “stolen” like a password, Multi-Factor Authentication can help prevent a wide variety of cybersecurity attacks.
#5. Train Employees to Spot Vishing and Other Cybersecurity Attacks
Best practices in cybersecurity are constantly evolving in response to new threats. Employees need to keep up! This is especially important in a remote work setting, where employees might not have immediate access to the IT team to address security concerns.
Ensure that your cybersecurity training curriculum includes an overview of good password management, along with how to identify potential phishing and vishing attacks. Consider video conferencing to conduct training so that employees have opportunities to ask questions and interact with the IT team.
#6. Encourage a “No-Trust” Mindset
A “no-trust” mindset sounds like the opposite of what you’d want to foster in your organization, but it’s important for security. Teach employees not to trust unexpected phone calls from people they don’t know, even if the person claims to be part of your organization. Instruct them to hang up and call back from an independently verified phone number--not the one provided by the caller.
After all, vishing scammers have been known to impersonate an organization’s own employees using a spoofed phone number.
#7. Choose the Right VoIP Provider
While your VoIP provider can’t stop your employees from answering vishing calls, it can help protect your organization in other ways. Look for a provider that embraces high standards for maintaining security.
The best VoIP providers also implement additional security options, from managed firewalls and Intrusion Detection Prevention Systems (IDPS) to Distributed Denial of Service (DDoS) and Security Information and Event Management (SIEM) to protect their underlying network. Seek a VoIP solution that includes Security Operations Center (SOC) support for event notification and remediation.